Penetration Testing_
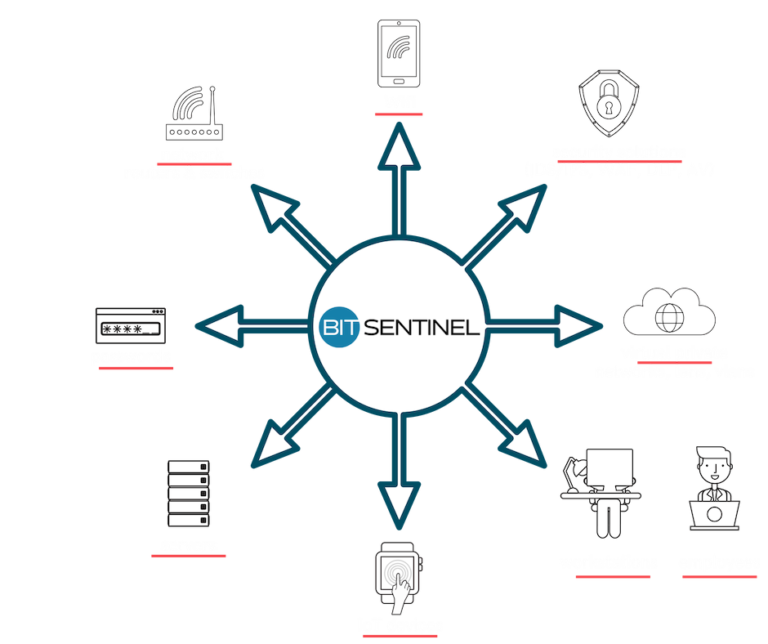
We help companies like yours discover, prioritize, and effectively remediate potential cybersecurity threats.
If you find yourself struggling to prioritize improvements to your organizations’ cybersecurity setup, you should know you’re not alone.
Many IT managers, CIOs, and CISOs are deeply worried about their company’s resilience to cyber attacks, given the current threat environment. Most of them also have trouble getting the resources they need to solve pressing issues before they turn into data breaches and company-wide crises.
This is precisely why more organisations like yours are using penetration tests to evaluate the security of their IT infrastructure in a safe and instructive way.
Penetration testing - demystified
When security experts conduct penetration tests, they simulate cyber attacks, attempting to uncover and safely exploit a company’s system vulnerabilities.
They do so without compromising the availability of the systems and confidentiality of information so businesses can continue to operate as usual.
During a penetration test, infosec professionals leverage their ethical hacking expertise to reveal:
- weaknesses in your infrastructure setup
- flaws in the operating systems, services, and applications
- improper configurations
- risky end-user behavior
- logic flaws in the applications’ business processes
- weak credentials that cyber criminals can use for malicious purposes
- hijacking and plenty more details.
This enables them to proactively address critical security weaknesses, mitigate them before attackers take a swing at them and avoid any downtime cost.
Vulnerability assessments are part of penetration tests.
Pentesting provides a more detailed outlook and is done manually, by specialists. That’s because it removes false-positives which makes it easy for you to focus your resources on fixing the right issues.
Moreover, a human can detect any subtle changes, logic flaws and abnormal behaviour that automatic tools and technologies won’t be able to catch in a timely manner.
Throughout our history of doing penetration tests, we’ve seen our customers make great progress by applying the actions we recommended.
For example, subsequent pentesting engagements we did for them in the following years uncovered no critical or high risk vulnerabilities. When you act on threat data, results become obvious.
You should contract a penetration test...
- at least every 12 months, as data flowing through the business tends to accumulate errors and vulnerabilities on both the tech and human side
- when you introduce new applications or new equipment into your network, to ensure they don’t bring new vulnerabilities
- when you make significant changes to how the applications in your organization work
- after you’ve applied security patches or implemented new security solutions to find out if they’ve been properly implemented
- when you relocate to a different office space which involved a new tech and physical setup with new security challenges
- when you make important updates to your internal policies and procedures that inherently impact your overall security level.
Make well-informed decisions and be agile in protecting your critical assets
We compiled a list to look for when you decide to perform a penetration test against your web application, network, infrastructure, workstations, wifi networks or employees. This will also help you better understand the advantages of performing this type of security audits.
Our team tests your security controls throughout the entire company to reveal crucial vulnerabilities that require urgent remediation.
Expert validation helps you prioritize security issues accurately, so you have a clear plan to follow once the pentest is completed.
Assigning severity levels to your security issues is a key aspect but we go further than that.
Our penetration tests also include an assessment of how attackers could combine and exploit low-risk vulnerabilities in such a way that they end up creating higher-risk ones.
When you perform a pentest with Bit Sentinel, our team ensures you get the highest value for your investment.
That means we don’t hand you an indiscriminate list of vulnerabilities. Instead, we provide you with a prioritized action-plan that includes context and actionable recommendations.
Working with us means you’ll always have a single point of contact to answer all your questions and guide your decisions. What’s more, that person is an infosec professional who is directly engaged in the pentest.
This means you get knowledgeable answers and competent input throughout the entire project.
Pentesting can make cybersecurity a significant competitive advantage for your company. When you identify and address security gaps before a malicious hacker does, you’re the one in control.
A strong grasp of your environment enables you to determine clear priorities and removes a great deal of ambiguity from your workflow. You can focus and be more effective in your work, as can everyone else in the company.
The penetration tests we do at Bit Sentinel go far beyond vulnerability assessments. During the project, we manually review and remove false-positive results so, you get a sharp image of the threats targeting your organization.
This makes it easier for you to tackle specific challenges and saves time you might spend on additional verification.
Moreover, we use human intelligence, experience and expertise that can detect any subtle changes, logic flaws and abnormal behaviour that automatic tools and technologies won’t be able to catch in a timely manner.
No two companies are alike which is why we don’t use template reports and recommendations. The remediation guidance we provide is never generic but rather adapted to your context.
Each pentest the Bit Sentinel team handles includes tailor-made suggestions that focus on your company’s specific needs and challenges.
A professional penetration test assesses how effective your current security controls are. As a result, you can clearly evaluate how adequately your company has built and deployed both proactive and reactive defenses.
Armed with these insights, IT and security leaders, like yourself, can make better decisions going forward.
Knowing where and how your cybersecurity setup might fail is not enough. Malicious hackers are increasingly skilled and creative in their approaches.
To beat them at their own game, we use similar tactics when we simulate cyber attacks during pentesting. Our goal is to determine whether your critical data is actually at risk and specifically how it’s exposed.
- Do your colleagues in marketing or HR know what to do when they get a phishing email?
- Do decision-makers have a crisis plan to handle a potential data breach?
- Do providers know who to contact in case they get compromised and it affects you too?
- How long does it take for your staff to identify the attacks performed in a penetration test?
Penetration tests help you answer these questions and more. You also understand the knowledge gaps throughout your organization, so you can plan to solve them.
At Bit Sentinel, besides advising you on technical implementations, we also train your team to recognize, react and respond to cyber threats.
Successful cyber attacks often have far-reaching consequences that business leaders did not anticipate. We’re here to help you avoid ending up in this situation.
Our team of infosec pros enable you to accurately measure risk and evaluate the potential impact of common cyber attacks and other security incidents.
On-the-ground knowledge paints an accurate picture of your current context and helps you balance quick fixes and long-term solutions.
When you assign a monetary value to real-world effects of data breaches and other forms of malicious hacking, you have strong arguments to present to your superiors.
In order to maintain your board’s engagement with cyber risk management, you need explicit proof that the issues are worth addressing promptly. We supply the data you need, complete with context and prioritization.
A good strategy to keep cyber criminals from compromising your critical assets is to build your security setup in layers.
When we simulate realistic attacks against your defenses, we try to infiltrate your company from various angles. Whether the attackers target an employee, a customer or a technical security control, we inform you of what might happen and how you can prevent privilege escalation or lateral movements in your network.
Contracting a pentest informs you whether your organization’s defenses are focused on protecting what matters.
Bit Sentinel security experts simulate the tactics, techniques, and procedures that real-world cyber criminals use when targeting your assets.
Our goal is to give you the data and indications you need to keep business-critical assets safe and confidential.
Many large organizations are required by law to prove that they’re proactively managing their cybersecurity program. Even business partners sometimes ask for it because security is now a key trust factor for big engagements and investments.
Use a penetration test to identify gaps in your information security compliance. Solve them to become and remain compliant with the latest regulations. The security audit that’s part of the pentest supports your efforts and provides the starting point to produce or improve your risk management policies.
In order to anticipate which business asset malicious hackers will target in your company, you have to understand their incentives and how they operate.
At Bit Sentinel, we go to great lengths to explain current threats and tactics, supporting you to build your defenses adequately.
When we simulate attacks, we also observe and record how long it takes for your security team to realize there’s a breach and act to mitigate its impact.
Pentesting is one of the most effective ways to test your own team’s response time and find the most powerful ways to improve it.
Here’s what a Bit Sentinel penetration test includes
In this aspect of the pentest, Bit Sentinel ethical hackers focus on discovering what information an attacker can get if they successfully breach your network perimeter. Moreover, this scenario also exposes insider threats, such as disgruntled employees, suppliers or customers that a malicious hacker may target.
Here are just some of the elements our experts will strive to evaluate:
- publicly available information about your company and your network (IP addresses, domain names, host names, etc.)
- email addresses and personal information about your company’s leaders (CEO, CFO, IT managers, etc.) that can be used in subsequent stages
- repositories of stolen data from a previous breach that might include details about your company which an attacker might use
- the configuration of the network and how security technologies, such as firewalls, Intrusion Detection Systems (IDS) react to different threats
- network mapping, OS fingerprinting, and network segmentation
- the ability to capture data as it travels across a network (also known as Man-in-the-Middle attacks or traffic sniffing)
Network perimeter pentesting also involves a full vulnerabilities scan, filtering the results, and cleaning up false positives.
Additionally, our team realistically simulates what happens if a malicious actor gets behind your firewall and compromises a user-level account.
We perform advanced penetration testing for cloud services, with a strong focus on:
Public cloud environments: AWS, GCP, Azure – covering IAM misconfigurations, exposed services, insecure storage, privilege escalation paths, and more;
Private cloud & hybrid infrastructures: including VMware, OpenStack, and on-prem deployments;
Microservices & API security: testing REST/gRPC APIs, service-to-service communication, and token handling;
Containerized environments: Docker and Kubernetes (K8s) – analyzing cluster misconfigurations, RBAC flaws, exposed dashboards, and lateral movement across pods/namespaces;
CI/CD pipelines: review of build, deploy, and secrets management processes;
Cloud-specific attack paths: including SSRF to metadata abuse, exposed credentials, and misused cloud-native services.
We simulate real-world attacker scenarios to identify security gaps in your cloud architecture and help you remediate them before they are exploited.
An important part of the penetration tests we perform is uncovering vulnerabilities in web and mobile applications. The more apps your company uses, the higher the risk, making a penetration test an essential requirement.
We focus on in-depth code reviews to:
- identify security issues in the application code;
- inspect apps throughout the Software Development Life Cycle (SDLC);
- verify if best practices are applied;
- provide actionable recommendations for your development team to improve code and prevent vulnerabilities.
We conduct comprehensive security assessments to:
- discover weaknesses that attackers could exploit;
- assess risks of unauthorized access or critical data exposure.
Here’s a list of the most common web application vulnerabilities:
- SQL Injection
- Cross-Site Scripting (XSS)
- Unsecured Authentication
- Sensitive Data Exposure
- Security Misconfiguration
- Weak Cryptography
(and many more; unfortunately, the list is long)
Why application testing matters
Testing applications is a thorough and detailed process. It requires:
- looking at technical details with precision;
- understanding usage patterns;
- evaluating the bigger business context around heavily used applications.
Maintaining flexibility while preserving security is a key objective for many organizations.
Our approach at Bit Sentinel for mobile penetration testing includes:
comprehensive mobile device testing
we assess how secure the mobile devices in your company really are;
we evaluate potential risks introduced by device configurations and usage habits.
mobile application security review
we perform in-depth security code reviews of installed apps;
we analyze both frequently used and less-used applications;
we identify vulnerabilities and weaknesses attackers might exploit.
Why mobile penetration testing matters:
mobile devices and applications are often prime targets for cyberattacks;
security gaps can lead to:
data leakage
unauthorized access
increased attack surface across the organization
Through mobile penetration testing, our goal is to:
give you an accurate understanding of the risks mobile devices and apps introduce;
provide prioritized findings so you know where to focus first;
recommend effective solutions to help you mitigate and reduce risk.
We offer specialized penetration testing for LLM/AI applications, focusing on real-world threats and the OWASP Top 10 for LLMs, including:
Prompt Injection (direct and indirect)
Training Data Poisoning
Model Denial of Service (DoS)
Sensitive Information Disclosure
Insecure Plugin or Tooling Integration
Excessive Agency and Overreliance
Supply Chain Vulnerabilities in AI Pipelines
Model Theft or Extraction
Insecure Output Handling
Data Leakage via Embeddings or Logs
We test both the LLM backend and its integration into your app (APIs, agents, chat interfaces, tools), identifying risks across the full stack—prompt-to-code. This helps you ensure safety, privacy, and robustness of your AI-driven systems.
When you work with Bit Sentinel for a penetration test, we also assess how secure your wireless solutions are. This helps you understand how well your company’s data is protected in transit, as well as how safe the systems connected via wireless technology really are.
We analyze wireless networks to identify issues such as:
- unsecured configurations
- weak authentication methods
- vulnerable protocols
These gaps can allow attackers to gain access to your wireless network, even from outside your building.
Beyond the Office
Risks don’t stop at your company’s perimeter. Employees using mobile devices on insecure, open guest networks (during meetings outside the office or while traveling) can also introduce entry points for attackers.
As part of our penetration tests, we also closely examine and probe embedded devices and IoT (Internet of Things) devices spread throughout your organization.
Because IoT includes software, sensors, actuators, and because they’re always connected to interact and exchange data. It’s our job to determine if they’re safe to use and if data can flow through them in a secure manner.
Consequently, we assess your IoT devices by attempting to:
- Exploit the embedded firmware
- Control the devices by injecting unsolicited malicious commands
- Modify data sent from these devices.
The objective is to help you understand if these devices can ensure your security standard is preserved. At the same time, our goal is to confirm if the commands and information issued from any of your IoT devices are legitimate.
With malicious hackers renting botnets rather cheaply and launching Distributed Denial of Service (DDoS) attacks that crush defenses and take down websites used by millions, it becomes essential to validate if your company can withstand such an attack.
As part of our process, we test your predisposition and your network assets’ behavior to many types of Denial of Service attacks. At the same time, we examine your DDoS defenses or applications in various scenarios to see if your network architecture is resilient and if your protection systems work as intended.
Penetration testing standards
At Bit Sentinel, we use the best practices and standards in information security to ensure that you get the biggest value from every type of penetration test we do:
- Network and Information Security (NIS) Directive - NIS1 & NIS2
- TIBER-EU
- NIST (National Institute of Standards and Technology)
- OSSTM (Open Source Security Testing Methodology)
- OISSG (Open Information Systems Security Group)
- OWASP (Open Web Application Security Project)
- CERT Coding Standards
- Penetration Testing Standard
- Penetration Testing Framework
- Norm 4 ASF/2018
- Network and Information Security (NIS) Directive
- Secure Software Development Lifecycle (S-SDLC)
- Mobile Security Testing Guide (MSTG)
- Technical Guide to Information Security Testing and Assessment (NIST 800-115)
- Information Systems Audit and Control Association – ISACA
- Penetration Testing Execution Standard (PTES)
- Information Systems Security Assessment Framework (ISSAF)
Penetration testing expertise, backed by certifications
Our team combines hands-on penetration testing skills with leading industry certifications:



















The 7 stages of a Bit Sentinel penetration test
- A meeting or a call with one of our certified pentesters
- Setting expectations
- Define the scope and goals of the pentest
- Define the list with all systems that will be tested
- Determine included and excluded activities
- Select the pentesting methods to be used
- Sign consent forms between your company and our team
Gather intelligence to better understand how a target works and its potential vulnerabilities based on Open Source Intelligence (OSINT) and other in-house developed methodologies
- Gather relevant documentation and information
- Identify and categorize assets
- Identify and categorize threats and groups of threats
- Map threat groups against assets
- Based on the customer’s needs, in this phase the specialists will perform various tests in order to uncover:
- Web Application vulnerabilities
- Network assets vulnerabilities
- Infrastructure Design issues
- Memory-based vulnerabilities
- Wi-Fi vulnerabilities
- Zero-Day Angle
- Physical vulnerabilities
- Social engineering
- Gain access by simulating realistic attacks such as vulnerabilities defined in OWASP TOP 10 (for eg. Cross-site scripting, SQL injection) and others
- Remove any false positives
- Escalate privileges or achieve lateral movement in the network
- Attempt to steal data, intercept traffic, etc., to understand the damage an attacker can cause
- Try to achieve a persistent presence in the exploited system to see if an attacker who gains access can maintain it for a longer time without being noticed
- Simulate advanced persistent threats
- Creating the pentesting report which includes a detailed description of all the activities and the discoveries that resulted from them
- Define the recommendations for patching vulnerabilities and creating the processes that protect your company against future attacks
- Detailed explanations to provide you with the context you need to understand how you can use your resources to address cybersecurity priorities
- Develop the Executive summary
What may be helpful to know is that we include a retest of your system in the original penetration test price. This helps you track your progress after you’ve implemented the remedial actions we recommended.
What you get after a Bit Sentinel penetration test
Once the penetration test concludes, we provide you with a useful and actionable report structured to meet international standards, that includes:
- Limitations Regarding the Disclosure and Use of This Report
- General Introduction - setting the context
- Executive Summary - the high-level overview of our findings
- Methodology - testing methodologies used
- Conducted Tests - the list of tests we performed and what we focused on finding by using them
- Identified Vulnerabilities - list, distribution, risk scoring and the technical documentation you can use to recreate our findings
- Detailed Report of Each Vulnerability - fact-based risk analysis to validate results
- Conclusions - tactical guidance for immediate improvement and strategic recommendations for long-term enhancements.
Find out which pentest approach works for you
A red team penetration test is an advanced security assessment where a specialized team simulates real-world attacks to test how well an organization can detect, respond to, and recover from them.
The experts at Bit Sentinel conduct red team penetration tests aligned with the Threat Intelligence-Based Ethical Red Teaming (TIBER-EU) framework developed by the European Central Bank. This framework is designed to enhance the cyber resilience of financial institutions and other critical entities across Europe.
A red team test aligned with TIBER-EU is defined by the following key elements:
- threat intelligence-driven: scenarios are based on real and relevant threats specific to the organization’s sector, region, and critical services.
- advanced attack simulation: the red team emulates tactics, techniques, and procedures (TTPs) used by sophisticated threat actors (e.g., APT groups).
- focus on critical functions: the goal is to test the resilience of processes and services that are vital for the organization and its customers.
- realism and stealth: the exercise often runs covertly, so defenders (Blue Team) are unaware of the exact timing or scope, simulating a real-world attack.
- structured governance: TIBER-EU ensures proper oversight, standardized reporting, and controlled execution to minimize risks while maximizing learning.
Penetration testing vs red team penetration testing
A penetration test is:
- typically scoped to specific systems or applications;
- identifies technical vulnerabilitiesl
- often done with defenders aware of the test.
A red team penetration testing aligned with TIBER-EU:
- has a broader scope: people, processes, and technology.
- simulates advanced persistent threats (APTs).
- tests detection and response, not just prevention.
- follows a standardized, regulator-recognized methodology.
In this setting, the penetration testing team has no prior knowledge of the company they’re about to evaluate.
This enables Bit Sentinel cybersecurity professionals to:
- Launch controlled attacks against the tested systems to uncover security flaws in a realistic manner
- Uncover how lower-risk vulnerabilities exploited in a particular sequence lead to higher-risk vulnerabilities
- Identify vulnerabilities that may be difficult or impossible to detect with automated network or application vulnerability scanning software
- Scale pentesting methods to large infrastructures while keeping software confidential
- Mimic attackers’ behavior in a lifelike manner to identify weaknesses in your infrastructure and any of your services.
This version of pentesting is also known as a glass box, structural, clear box, and open box testing. Its name implies that you provide complete knowledge of your infrastructure to the ethical hackers who perform the test. This often includes network diagrams, source code, ranges of IP addresses and more.
Armed with this knowledge, the engineers on the Bit Sentinel team identify weaknesses before conducting a comprehensive audit to identify all other vulnerabilities.
Knowing what a specific asset does is essential for white box penetration testing because it informed the tester if a program diverges from its intended goal.
Some of the benefits of white box pentesting include:
- Revealing errors in code without special access to tested assets
- Identifying points of failure faster to allow for prompt remediation
- Being an ideal fit for small-to-medium applications or less complex systems
- Revealing weak code sections that might fail under compromise attempts (see security code review).
If you’re looking for a complete and thorough examination of your vulnerabilities, we recommend both white box and black box tests.
Wondering if there’s a version in between white box and black box pentesting?
There is and it’s predictably called grey box testing.
This option blends tactics from both testing techniques and allows for a comprehensive perspective of your organization’s security level.
In this context, Bit Sentinel engineers examine the design documentation your provide about your network and prioritize tests targeting high-risk assets instead of working through this process themselves throughout the test.
Because of its highly focused approach, grey box testing is effective both from a cost and duration perspective. At the same time, our team can validate attack vectors and scenarios and minimize false positive results faster.
If you are looking for a result-oriented Penetration Testing that basically involves paying for security bugs found, instead of our time spent researching and identifying them, Bug Bounty Penetration Testing is for you.
Instead of paying a fixed fee, we will charge a fee per vulnerability discovered, relevant to its class of vulnerability and the manner in which it is found.
If no security vulnerabilities are discovered during the engagement period, we do not charge you anything. Also, duplicate issues across different systems or the same issues found repeatedly are only charged once.
Bit Sentinel will ask you to establish a “Maximum” threshold amount you are willing to spend on this engagement. If the threshold is reached, you can decide if we close the engagement or continue researching other vulnerabilities.
Choosing Bit Sentinel for your penetration tests means you get:
- Full transparency over the penetration testing process
- Certified infosec professionals who focus on one customer at a time
- Fair pricing that doesn’t change, including clear terms and conditions
- Thorough testing without downtime and business impact
- Professional and responsive support from highly qualified engineers
- A single point of contact to keep communication smooth and effective
- Actionable reports and guidance to make the best decisions for your organization
- A re-test included in the original price, performed after you’ve had enough time to apply the recommendations included in our report.
What our clients say:
See how our penetration testing services have helped organizations strengthen their security:

